this post was submitted on 29 Mar 2025
986 points (98.8% liked)
[Moved to [email protected], check pinned post.] iiiiiiitttttttttttt.
919 readers
1 users here now
you know the computer thing is it plugged in?
Moved to [email protected].
founded 2 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
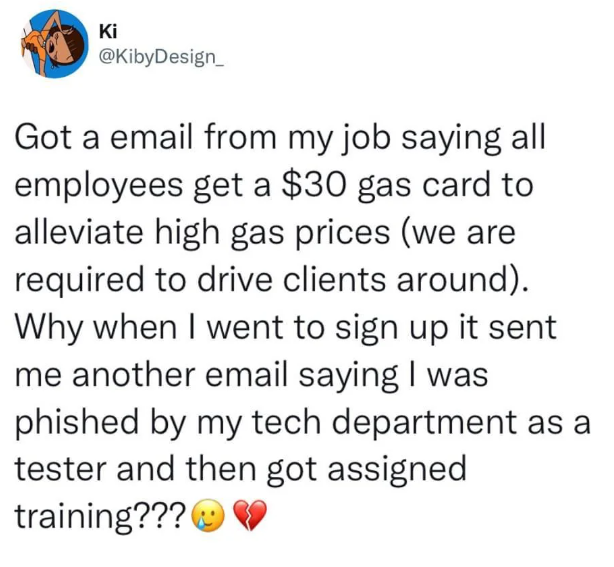
You might have a lot of phishing emails that the company filters out without you ever seeing them. For these tests, they do things to make sure this email will get through, even if the automated filters would have otherwise blocked it.
That's a good point; my company actually does implement something like this, though it invites intervention from the recipient for confirmation. I have previously received e-mail notifications stating that an e-mail has been 'held' as being suspicious and provided me an option to 'release' the e-mail (in these cases the e-mails were genuine and known in advance to me).
Of course, I have no simple way to determine if there is also an additional hard filter that blocks out obvious phishing with no notification to the end user.
There are likely two things going on.
One is a hard block for phishing, ones you will never see, never be alerted of, and never be told about unless you go digging for a missing email you know should have come through.
The other is a soft block for spam. You will likely get an email about the spam being quarantined with the option to release the spam into your inbox.
If the phishing emails were shown as quarantined, you’d end up with hundreds of quarantined emails a day for anyone with a public facing name. Our CFO for instance gets the most out of anyone in the company, numbering in the thousands.
This is a good explanation. I can see how a multi-tiered approach like this makes sense, particularly for those most public-facing. Thanks.